Risk Management for Dual-Use Potential in Life Science Research
Contents
- Preface
- Abbreviations and Acronyms
- Chapter 1 – Introduction
- Chapter 2 – Dual-Use Potential
- Chapter 3 – Risk Management Process
- Chapter 4 – Opportunities for Risk Management Throughout a Research Project
- Chapter 5 – References and Resources
- Appendix A – International Initiatives Related to Dual-Use Potential
Preface
In Canada, facilities where Risk Group 2 (RG2), RG3, and RG4 human pathogens or regulated toxins are handled and stored are regulated under the Human Pathogens and Toxins Act (HPTA) and the Human Pathogens and Toxins Regulations (HPTR). The handling and storing of imported RG2, RG3 and RG4 animal pathogens or parts thereof (e.g., toxin) are regulated under the Health of Animals Act (HAA) and the Health of Animals Regulations (HAR).
Under the authority of the HPTA and the HPTR, the Public Health Agency of Canada (PHAC) regulates the handling and storing of human pathogens and toxins. Furthermore, under the HAA and the HAR, PHAC regulates the importation and subsequent transfer or receipt of indigenous terrestrial animal pathogens or parts thereof in pure culture or in a non-animal matrix (e.g., human, plant, food, or environmental sample).
The Canadian Food Inspection Agency (CFIA) regulates the importation and subsequent transfer or receipt of the remaining animal pathogens or parts thereof (e.g., toxin) under the HAA and the HAR. This includes CFIA Designated Terrestrial Animal Pathogens (CD-TAPs), any terrestrial animal pathogen when in animals, animal products, and animal by-products (e.g., tissue, serum), bee pathogens, and aquatic animal pathogens. CD-TAP is a term used to capture foreign animal diseases (FADs), emerging animal diseases (EADs), and non-indigenous terrestrial animal pathogens under CFIA’s authority.
The following figure depicts the document hierarchy used by PHAC and CFIA to oversee biosafety and biosecurity operations. Each tier of the pyramid corresponds to a document type, with documents increasing in order of precedence moving upwards. Acts and Regulations are found at the top of the pyramid, as they are the documents that convey PHAC’s and CFIA’s legal authorities. Risk communication tools and technical documents are found at the bottom of the pyramid, as they are only intended to summarize recommendations and scientific information.
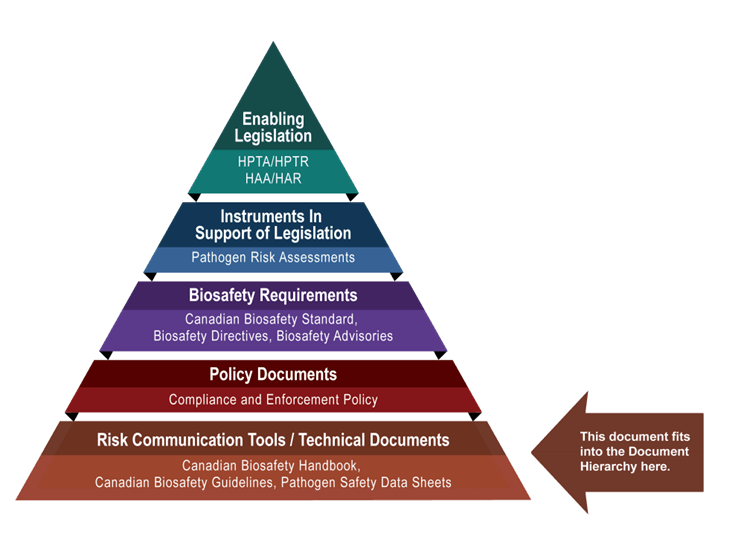
The Risk Management for Dual-Use Potential in Life Science Research guideline was developed by PHAC and CFIA as part of a series of electronic publications that expand upon the biosafety and biosecurity concepts discussed in the Canadian Biosafety Standard, Third Edition (CBS). This guideline provides information and considerations on how to assess dual-use potential in life science research involving pathogens, toxins, or other biological material, and how to manage associated risks.
back to topAbbreviations and Acronyms
|
Acronym |
Term |
|---|---|
|
AI |
Artificial intelligence |
|
BSO |
Biological safety officer |
|
CBS |
Canadian Biosafety Standard, Third Edition |
|
CBSA |
Canada Border Services Agency |
|
CD-TAP |
Canadian Food Inspection Agency designated terrestrial animal pathogen |
|
CFIA |
Canadian Food Inspection Agency |
|
CL |
Containment level (i.e., CL1, CL2, CL3, CL4) |
|
GAC |
Global Affairs Canada |
|
HAA |
Health of Animals Act |
|
HAR |
Health of Animals Regulations |
|
HPTA |
Human Pathogens and Toxins Act |
|
HPTR |
Human Pathogens and Toxins Regulations |
|
IBC |
Institutional biosafety committee |
|
IT |
Information technology |
|
PAO |
Plan for Administrative Oversight |
|
PHAC |
Public Health Agency of Canada |
|
RCMP |
Royal Canadian Mounted Police |
|
RG |
Risk Group (i.e., RG1, RG2, RG3, RG4) |
|
SOP |
Standard operating procedure |
|
SSBA |
Security sensitive biological agent |
|
WHO |
World Health Organization |
Chapter 1 - Introduction
The words with a dotted underline are defined in the found on the PHAC Training Portal.
in life science research refers to the qualities of a or , scientific method, intellectual property, or other related that allow it to be either used for legitimate scientific applications or intentionally misused to cause harm or . The potential for life science research assets to be misused by can lead to significant societal, legal, ethical, economic, safety, and security concerns.Footnote1
When conducting life science research, it is important to achieve a balance between:
- advancing life science research and technologies aimed at benefiting society (e.g., enhancing public health, helping the environment, promoting economic growth); and
- protecting the and the environment from potential associated with certain aspects of life science research that could be exploited to cause harmFootnote2
1.1 Scope
The Risk Management for Dual-Use Potential in Life Science Research guideline provides comprehensive guidance on how to identify, assess, and mitigate the risks associated with dual-use potential in life science research involving , and is meant to increase awareness on the topic. It aims to help in the evaluation of research activities involving biological material to determine the likelihood that an activity or its products could be misused to cause harm, and to provide strategies for mitigating identified risks. This guideline is also meant to promote the ethical and responsible conduct of research among scientists, educators, , (BSOs), funding organizations, and policy and decision makers.
The information provided in this document is intended as guidance only and is not meant to be interpreted as requirements. Alternative approaches may be used to meet the requirements specified in the Canadian Biosafety Standard, Third Edition (CBS).
1.2 How to Use the Risk Management for Dual-Use Potential in Life Science Research Guideline
A detailed list of all abbreviations and acronyms used throughout this guideline is located at the beginning of the document. Each word or term is spelled out upon first use, with the abbreviation or acronym immediately following in brackets. After its initial definition, the abbreviation is used exclusively throughout the remainder of the document. A comprehensive of definitions for technical terms is available on the PHAC Training Portal. Terms defined in the glossary appear with a dotted underline upon first use in the guideline. Where the guidance relates to a specific requirement in the CBS, the requirement matrix or matrices are referenced (e.g., CBS Matrix 4.1). A full list of references and other resources is provided in Chapter 5. Unless otherwise noted, all occurrences of “research” throughout this guideline relate specifically to “life science research involving biological material”.
back to topChapter 2 - Dual-Use Potential
In the past, dual-use potential has had detrimental consequences to public health and safety, the animal population, the environment, and national security. As it remains a global concern, it is critical that governments and authorities worldwide emphasize the need for formal oversight of dual-use potential.Footnote1
2.1 History
Dual-use potential in life science research was notably brought to the attention of the general public in 2001, after letters containing Bacillus anthracis spores (the causative agent of anthrax) were mailed to two United States Senators and several news media offices, resulting in the death of five people and the infection of 17 others.Footnote3 A subsequent investigation revealed that the spores originated from a US federal biodefense centre, and that the person accused of sending the letters was a scientist who had access to the bacterium and possessed the skills and knowledge necessary to produce the spores.Footnote3,Footnote4 Following this event, there have been additional instances that have highlighted concerns around dual-use potential in fields such as infectious disease, stem cells, , genetic modification of organisms, genomics, and synthetic biology.Footnote5,Footnote6 Since the COVID-19 pandemic, there has been increased interest in the mitigation of and risks around the world. Currently, there is a high degree of international concern surrounding activities and information that could lead to intentional or unintentional of pathogens with pandemic potential, which could significantly affect the health of humans and animals globally.
Table 2-1 presents examples of research activities that have gained international attention regarding the dual-use potential of pathogens, toxins, knowledge, techniques, or technologies. Many of these examples involve gain-of-function research, which includes the modification of biological agents to result in new traits or enhanced capabilities, often by increasing their ability to replicate and/or infect hosts. The goal of gain-of-function research is usually to increase the understanding of fundamental biological processes, such as how viruses spread, how they interact with host organisms, and how they evolve. It can also help researchers anticipate potential paths of evolution so they may develop countermeasures, such as vaccines or treatments, in response to emerging infectious diseases. However, it can raise ethical and safety concerns, particularly if the modified organisms may pose increased risks to public health or the environment.Footnote7
|
Research activity |
Dual-use potential |
|---|---|
|
2002 - Infectious poliovirus was synthesized de novo from the published structure and nucleotide sequence of the poliovirus genome. |
Intended benefit To demonstrate that viruses can be synthesized de novo (i.e., in the absence of a template). Concern for misuse The published methods could be used for the de novo synthesis of other viruses using publicly available genomic information. |
|
2002 - A variola virus (i.e., smallpox) protein was engineered using the sequence of a homologous vaccinia virus protein. The modified protein was identified as having the potential to increase the virulence of the vaccinia virus. |
Intended benefit To study the protein’s predicted role as a virulence factor. Concern for misuse The research information could be used to develop a more pathogenic strain of vaccinia virus (e.g., increased virulence). This research demonstrates the potential to synthesize variola virus virulence factors from lower risk pathogens in the same family. |
|
2005 - The influenza A(H1N1) virus responsible for the 1918 Spanish flu pandemic was reconstructed using a reverse genetics system.
|
Intended benefit To evaluate current and future public health interventions and understand the virulence of the influenza virus. Concern for misuse The reconstructed virus could be used to inflict harm (e.g., deliberate release, weaponization). The published methods could be misused to alter virus host range from avian to human. |
|
2011 - A strain of avian influenza A(H5N1) virus was modified to study and enhance airborne transmissibility in mammals. |
Intended benefit To study transmission and the development of pathogenic strains of avian influenza A(H5N1) virus in mammals to determine the virus’s pandemic potential. Concern for misuse The modified virus strain demonstrates enhanced transmissibility and could be used to inflict harm (e.g., deliberate release, weaponization). The published manuscript provides information about the genetic mutations that could enable the virus to become more transmissible in mammals. |
|
2018 - Horsepox virus, a previously extinct pathogen, was synthesized de novo using a publicly available genetic sequence and standard molecular biology techniques. |
Intended benefit To study the potential of a chimeric horsepox virus to be used as a live smallpox vaccine. Concern for misuse The published methods could be used to synthesize other poxviruses, including the eradicated variola virus. |
|
2019 - Ebola virus was generated de novo using Ebola virus sequences provided by organizations in the Democratic Republic of the Congo and a reverse genetics system.
|
Intended benefit To study the efficacy of experimental therapies and diagnostic tests against the strain responsible for the Ebola virus outbreak that began in 2018. To better understand the relation between strains responsible for Ebola disease outbreaks. Concern for misuse The published methods could be used to synthesize outbreak strains. |
|
2021 - Variants of the SARS-CoV-2 virus (the causative pathogen of COVID-19) were engineered using a reverse genetics system.
|
Intended benefit To help advance global research and response to the COVID-19 pandemic. Concern for misuse The published methods could be adapted to develop a variant that evades treatments and immunity. |
2.2 Oversight
Through various legislative mechanisms, the oversight of dual-use potential associated with pathogens, toxins, and related goods and technology is shared by several federal departments and agencies in Canada, including:
- Public Health Agency of Canada (PHAC)
- Canadian Food Inspection Agency (CFIA)
- Transport Canada (TC)
- Global Affairs Canada (GAC)
- Public Safety Canada (PS)
- Innovation, Science and Economic Development Canada (ISED)
- Canada Border Services Agency (CBSA)
- Royal Canadian Mounted Police (RCMP)
Examples of international initiatives that aim to identify and mitigate the risks associated with dual-use potential and information on the current global status of dual-use potential can be found in Appendix A.
2.2.1 Pathogen and Toxin Legislation and Regulation in Canada
A is required to perform with human pathogens and toxins unless an exclusion from the Human Pathogens and Toxins Act (HPTA) or an exemption from the licensing requirement applies.Footnote17,Footnote18 Even when exempt from requiring a under the HPTA, all persons knowingly conducting controlled activities with a human pathogen or toxin are required to take all reasonable precautions to protect the health, safety, and security of the public against the risks posed by their activities [HPTA 6].Footnote17
A or a is required for the importation or subsequent transfer of or part of one (e.g., toxin), or animals, animal products or by-products (e.g., tissue, serum), or other organisms carrying a terrestrial animal pathogen or part of one (e.g., toxin) under the authority of the Health of Animals Act (HAA) and the Health of Animals Regulations (HAR).Footnote19,Footnote20
It is the responsibility of licence and permit holders to understand their obligations under the HPTA, Human Pathogens and Toxins Regulations (HPTR), HAA, and HAR. As a condition of their licence or permit, in Canada where are must meet the applicable , , and specified in the CBS.Footnote21
2.2.2 Export from Canada
The Export and Import Permits Act (EIPA) implements export controls through Canada’s Export Control List (ECL). This Act is administered by GAC and enforced by CBSA and RCMP.Footnote22,Footnote23 The ECL includes two lists that are relevant in the context of this guideline:Footnote24
- the Dual-Use List (goods and technology), which fulfills Canada’s commitments under the Wassenaar Arrangement
- the Chemical and Biological Weapons Non-Proliferation List, which fulfills Canada’s commitments as a participant in the Australia Group
More information on these two lists and on export permits under the EIPA is available on the Global Affairs Canada website.
back to topChapter 3 - Risk Management Process
In Canada, a risk-based approach is used to support responsible research with biological material. Risk management associated with dual-use potential takes into consideration the degree of dual-use potential (i.e., high or low), the associated that are present, the likelihood and severity of an undesirable event, and mitigation measures that can be implemented. An effective risk management program aims to protect personnel, the community, and the environment from to, or release of, pathogens and toxins. It also aims to protect assets like research materials (including pathogens and toxins), animals, equipment, tools, procedures, and information against misuse.
Effective risk management is supported in part by complying with federal and applicable provincial or territorial legislative obligations, and licence or permit conditions, including applicable CBS requirements.
A Plan for Administrative Oversight (PAO) for pathogens and toxins in a research setting is a key component of an effective risk management program. A PAO is required for applicants who intend to carry out with human pathogens and toxins [HPTR 3]. The PAO sets out administrative measures, including internal accountability structures and systems (e.g., policies, procedures), for managing and controlling biosafety and biosecurity risks in life science research, including those associated with dual-use potential.Footnote25,Footnote26 Applicants are expected to describe the methods and mechanisms used within the organization to identify, assess, and mitigate risks associated with dual-use potential across the research lifecycle.
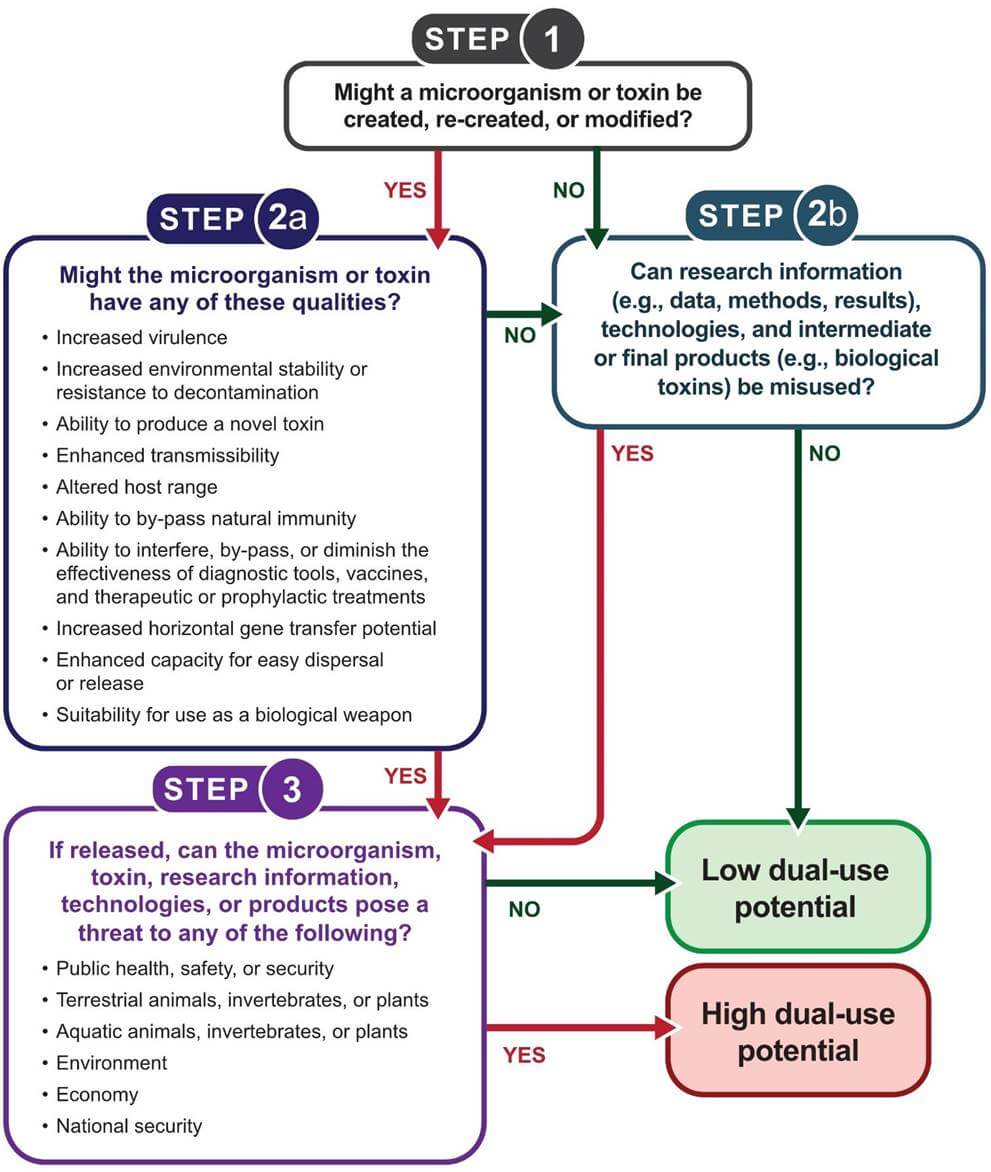
Dual-use potential is assessed by considering whether assets from life science research could be misused to cause harm or disease. Figure 3-1 can be used to guide the assessment of dual-use potential, which can be high or low. It is important to consider that changes in research plans or unexpected results may affect the degree of dual-use potential associated with a particular project. It is therefore important to re-assess the degree of dual-use potential periodically, even if it is initially established as low.
3.1 Hazard Identification
The first step in managing risks associated with dual-use potential is identifying hazards. Hazards are sources of potential damage, harm, or adverse effects. Those with dual-use potential include tangible and intangible assets that are used for legitimate scientific applications, but may also be intentionally misused to cause harm or disease to humans, the animal population, or the environment. Canada’s Sensitive Technology List outlines technology areas that could have national security implications if misused and are therefore considered to be sensitive by the Government of Canada.Footnote27 Activities are also considered as part of this step. It is important to note that hazards can influence the risks associated with other hazards. For example, two or more hazards may individually be associated with a low risk, but their combination may pose a medium or high risk.
3.1.1 Tangible Assets
Tangible assets have physical components. Examples of tangible assets associated with dual-use potential include biological materials, equipment, tools, and animals.
3.1.1.1 Biological Material
Dual-use potential in life science research is influenced by the inherent characteristics of pathogens and toxins in use. For example, certain 3 (RG3) and RG4 human pathogens and regulated toxins that have high or toxicity pose an increased biosecurity risk because they could be used as a biological weapon against the general public. These are referred to as (SSBAs). Similarly, certain terrestrial animal pathogens (e.g., CFIA designated terrestrial animal pathogens [CD-TAPs; captures , , and under CFIA’s authority]) are associated with high dual-use potential because they could be used as an agricultural bioweapon. This type of bioweapon could have negative implications on domestic food supply and subsequently on trade and the economy.
There may also be increased biosecurity risks and heightened dual-use potential associated with:
- a pathogen that has been eradicated or is extinct
- a pathogen or toxin that is novel (i.e., not previously identified)
- a pathogen or toxin that does not naturally exist in the environment (i.e., created or modified in the )
Dual-use potential can also exist for biological material that is not regulated (e.g., RG1 , nucleic acid sequences), as its manipulation could result in the intentional or inadvertent production of a regulated pathogen (i.e., RG2 or higher).
3.1.1.2 Other Tangible Assets
Other tangible assets (e.g., equipment, tools, animals) are important to consider when identifying hazards associated with dual-use potential. For example:
- Equipment and tools used in agricultural research could be misused to disperse .
- Emerging artificial intelligence (AI)-enabled technologies (e.g., robotic synthesis platforms, high-throughput screening devices) could be misused to facilitate the rapid production or modification of biological materials with dual-use potential.
- Animals infected with pathogens for research purposes could be intentionally released to cause harm to other animals, humans, or the environment.
3.1.2 Intangible Assets
Intangible assets lack physical substance. Those associated with dual-use potential include information and knowledge. Examples of intangible assets include:
- nucleic acid sequences of novel, emerging, or high risk pathogens (e.g., SSBAs)
- nucleic acid sequences of virulence genes
- details about technologies for pathogen or toxin delivery (e.g., aerosolization)
- instructions for laboratory techniques or technology
-
key elements of an organization’s
(e.g.,
, biosecurity plan), including:
- facility access instructions (e.g., related to keys, access cards, access codes)
- information regarding facility engineering designs and specifications (e.g., entry points, )
When identifying intangible assets as hazards associated with dual-use potential, it is important to consider whether the information generated (e.g., data, methods) could be used to threaten public health, safety or security, animal health, or the environment. For example, information could be applied to higher risk biological material, or it could be used to highlight a in pathogen oversight, public health capacity, or public safety preparedness.
Intangible assets have the potential to be misapplied or misused for malicious purposes. The following are examples of misapplication or misuse:
- Research information on the development of drug-resistant microorganisms intended to improve the understanding of resistance mechanisms and treatment could be used to develop organisms capable of evading available treatments.
- A method used for the dispersal of an RG1 biopesticide over crops may have the potential to be used for the dispersal of an aerosolized bioweapon.
- Information from research with low risk microorganisms could be applied to related high risk pathogens (e.g., across poxviruses).
- AI algorithms could be misused to create bioweapons.Footnote28 For example, advanced AI algorithms for genomic analysis can rapidly identify virulence factors and predict pathogen-host interactions. While these algorithms can enhance our understanding of pathogens, they could also be repurposed to design toxins or engineer tailored pathogens.
3.1.3 Activities
Regardless of whether a research activity involves a regulated material, or other biological material, dual-use potential can be influenced by the inherent aspects of research methods. Certain techniques and methods have a higher potential to be misapplied, even if the objective of the research was well-intended. The following are examples of techniques and methods that could have dual-use potential:
- research involving the passage of a pathogen in an animal host can be used to study the evolution of a pathogen or develop vaccines. However, such methods could also be used to select a pathogen strain with increased human and animal infectivity, , and transmissibility.
- Routine molecular biology techniques can be used for the de novo synthesis of a non-pathogenic microorganism (e.g., using oligonucleotides purchased from a commercial source, using published nucleic acid sequences for synthesis). These same techniques can also be used for the de novo synthesis of a pathogen that may otherwise be difficult to acquire.
- Serial passage and gene editing techniques are often associated with low dual-use potential (e.g., when used to create knock-out models to explore bacterial gene regulation). However, these techniques could also be applied in high dual-use potential gain-of-function research, which could present concerns related to public health, animal health, or the environment.Footnote29 Gain-of-function research aims to modify biological agents to create new traits or enhanced capabilities, often by increasing their ability to replicate and/or infect hosts (e.g., inserting a virulence factor into the genome of a host microorganism to develop a new or modified pathogen).
- Epigenetic manipulation could potentially be used to treat diseases by modifying gene expression patterns to improve the effectiveness of immunotherapies.Footnote30 However, it could also be misused to alter a host’s immune response or increase pathogenicity.Footnote31
- AI can be used to optimize models in diagnostic platforms. However, AI could also be misused to alter diagnostic outputs.
While all research with a pathogen or toxin has some degree of dual-use potential, research activities such as the following may contribute to the dual-use potential of a project:
- creating a new pathogen
- creating new intermediate or final products (e.g., toxins)
- performing activities with a new or emerging pathogen or toxin
- reconstructing an existing, extinct, or eradicated pathogen (e.g., de novo synthesis)
- using, developing, or enhancing, new or emerging techniques or technologies for pathogen or toxin delivery (e.g., new aerosolization technologies)
- modifying a pathogen or toxin (e.g., increasing drug resistance, immune evasion, pathogenicity, or virulence of a bacterium)
Modification of a pathogen or toxin may result in a higher risk group classification and may introduce other hazards. A review of existing scientific literature can help identify whether any unexpected results have been observed in similar studies (e.g., with related pathogens). Surrogate information from genetically related pathogens may be used to assess the risks of novel pathogens with unknown pathogenicity. Similarly, for novel toxins with unknown toxicity, surrogate information from a structurally similar toxin can be used.Footnote32,Footnote33,Footnote34 Even in the absence of such information, the planned activities can be assessed for their potential to produce unexpected results. The product of the activities can be evaluated by a for its potential to lead to a higher risk group classification. Additional information can be found in the Canadian Biosafety Guideline – Pathogen Risk Assessment.Footnote35
3.2 Risk Assessment
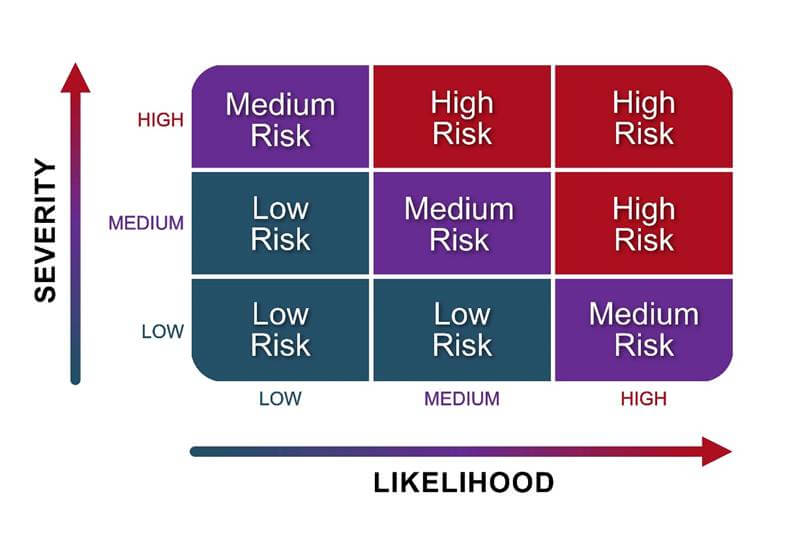
The risks associated with dual-use potential are determined by considering the likelihood of an adverse event occurring, and the severity of its consequences. A risk assessment matrix, such as the one in Figure 3-2, can help assess the level of each risk associated with dual-use potential of a research project. Even if the overall risk associated with dual-use potential is initially determined to be low, it is still important to monitor for changes as research progresses.
3.2.1 Likelihood Assessment
A likelihood assessment considers how likely it is for an event to occur. To help determine the likelihood of an event occurring, it is important to consider factors related to the motive, means, and capability to intentionally misuse pathogens, toxins, information, or technologies, including:
Laboratory conditions
- What laboratory conditions are needed to repeat or scale up the experiment?
- Would it be feasible to conduct the work outside of a fully equipped laboratory?
- Are the necessary laboratory conditions difficult to achieve, or can they be easily replicated in a makeshift laboratory?
- Could AI-enabled laboratory automation systems or lab-on-a-chip technologies facilitate experimentation by optimizing conditions, improving scalability, or reducing reliance on fully equipped laboratories?
Technical skills
- What technical skills are needed to repeat or scale up the experiment?
- Could the work be reproduced using AI or by a person with little scientific training or technical skills (e.g., AI-driven automated synthesis platforms reducing the need for specialized expertise)?
Resource acquisition
- Are the materials, tools, and equipment necessary to perform the experiment expensive or highly specialized?
- Are the resources, tools, and equipment regulated (e.g., equipment on the Australia Group’s export control lists) or available for purchase by the general public?
- Could specialized components be 3D printed?
- Could the research activities be contracted out under false pretenses?
Application to higher risk organisms
- Could information or techniques associated with lower risk organisms (e.g., horsepox virus) be easily applied to higher risk organisms (e.g., variola virus)?
Timeframe
- Could the timeframe to produce pathogens or toxins be shortened (e.g., due to access to large scale biotechnology equipment or AI technologies)?
- Could the asset (e.g., pathogen, toxin, research results, information, technique) be misused in its current state, or are refinements needed before it can be used to cause harm?
History of occurrence
- Has misuse involving the asset or a similar asset (e.g., pathogen, toxin, information, technique) occurred previously within the organization, region, country, or elsewhere globally? If so, how often has it occurred?
Motive
- How interested or motivated could an adversary be in obtaining the pathogen, toxin, information, or technology for malicious purposes? Adversaries may include personnel, contractors, foreign investors, research partners, or activists without a .
- Is there evidence that the research may be of interest to adversaries (e.g., reports or statements from intelligence sources like the Canadian Security Intelligence Service and the Communications Security Establishment Canada, research security statements from the Government of Canada)?Footnote36,Footnote37
3.2.2 Severity Assessment
When assessing the severity of potential consequences associated with a pathogen, toxin, technology, or information being released or misused, it is important to consider the impact on the following aspects:
Human and animal health
- What amount of pathogen or toxin causes infection, disease, or ?
- How transmissible is the pathogen between and within species (e.g., humans, animals)?
- What is the severity of infection, disease, or intoxication associated with the pathogen or toxin (e.g., does it result in serious disease or death)?
- What impact would the research have on infection control measures, medical management and treatment, disease surveillance and detection, or of a pathogen at a regional, national, or global level?
- Are effective vaccines or preventive and post-exposure treatments available to reduce the severity or transmission of infection, disease, or intoxication?
Environment
- Can the pathogen survive, persist, disperse, or proliferate in the environment?
- Can the pathogen or toxin alter ecosystems, displace species, negatively impact agriculturally important crops, or adversely affect biodiversity?
Public perception
- Are the risks associated with the scientific research readily understood by the general public, the media, or others without an education in science?
- Could the research be the subject of misinformation?
National security and economy
- How would widespread infection, disease, or intoxication compromise critical infrastructure or the economy (e.g., agriculture, hospitals, importation and exportation of goods)?
3.3 Risk Mitigation
Everyone has a responsibility to mitigate risks associated with the knowledge, information, methods, products, or technologies they develop. Risk mitigation is an ongoing process in which specific measures are put in place to minimize the likelihood of an or the severity of its consequences if one occurs. Appropriate mitigation measures depend on the risks identified and can be physical or operational in nature. For example, mitigation measures might include the implementation of codes of conduct, personnel screening, physical or logical security barriers, management, destruction or of materials, cybersecurity measures, and emergency or incident prevention measures.
Once risk mitigation measures are implemented, they are overseen by the appropriate authority (e.g., laboratory personnel, principal investigator, BSO, senior management, the institutional biosafety committee [IBC], regulatory authorities, other oversight bodies). It is important to note that unless an activity is not conducted, risks cannot be completely eliminated, regardless of the mitigation strategy.
The goal of risk mitigation is to reduce the identified risks to a level that has been deemed acceptable by an organization’s risk tolerance threshold. The risk tolerance threshold is established by the organization and is aligned with internal policies, which support compliance with applicable legislation and regulations (e.g., HPTA, HPTR, HAA, HAR).Footnote38 Considerations that may also be reflected in the established risk tolerance threshold include:
- perceived risk (e.g., by the general public)
- reputational risk (e.g., loss of credibility within the scientific community)
- financial risk (e.g., loss of funding)
Risk mitigation can also be supported by the implementation of international standards and guidelines (e.g., ISO 35001 - Biorisk Management for Laboratories and Other Related Organisations).Footnote39
3.3.1 Biosecurity Measures for Intangible Assets
When implementing mitigation measures to protect against misuse of intangible assets, it is important to consider how they could be accessed. For example, adversaries may bypass operational or physical security measures to access, use, modify, disclose, or destroy assets (e.g., via cyber attacks, unauthorized information technology [IT] network access, or breaking through physical barriers).
Mitigation measures to prevent adversary access to intangible assets may include:
- security controls, such as more stringent personnel security screening, or increased physical security measures in parts of a facility where is kept
- (SOPs) to help secure assets when not in use
- training on intangible assets to help personnel recognize the sensitive information they have in their possession, and the security measures needed to protect it
Personnel may have access to intangible assets (e.g., information, knowledge) when they have direct or indirect involvement in a research project. Robust training programs on intangible assets cover the importance of a clean desk policy, storing sensitive information in secure locations, managing keys and access cards, and following SOPs to secure information on the organization’s IT network, hard drives, external storage devices, and other electronic record storage locations. The training program can also promote practices that mitigate the risks of cyber attacks, such as phishing scams and malware attacks. For example, an organization could train personnel to use strong passwords to log into accounts, and to encrypt sensitive information before sharing with collaborators. Training sessions on intangible assets can also include an organization’s communication plan for sharing sensitive information (e.g., in abstracts, presentations, posters), as determined by the biosecurity plan. Additional information on biosecurity measures for 4 (CL4) can be found in the Biosecurity Addendum to the Canadian Biosafety Standard, Third Edition (the Biosecurity Addendum).Footnote40
3.3.2 Communication Plan
A communication plan is an important consideration to help mitigate risks associated with dual-use potential. By identifying how, when, to whom, and what information may be communicated, the communication plan provides a framework to help protect sensitive information and communicate research details responsibly.
Target audience
The communication plan can identify with whom information may be shared. The target audience may include the scientific community, the general public, or a small group of trusted stakeholders or collaborators.
Timing
The communication plan can outline when personnel may communicate results or information. For example, it can provide considerations and SOPs for reactive versus proactive messaging, as well as pre-publication or pre-communication review processes that help determine strategic timing to release communications responsibly.
Proactively releasing media communications to the general public can help highlight the value of research and the mitigation measures in place to improve public understanding. This can help prevent the spread of misinformation (i.e., accidental falsehood shared without malice) and disinformation (i.e., deliberate falsehood shared with malicious intent). It is also important to keep in mind that research plans and findings are often communicated at many points throughout the research process, and not only after completion. Beyond publication in a scientific journal, information may also be communicated as part of:
- project concept and design
- funding application
- institutional approval
- literature review and experimental process
- development of manuscripts or other means of communicating research results (e.g., preprint release, conference presentation, patent application)
- publication of information on funding databases available to the public
- funding progress reports
Means of communication
Information or results regarding life science research can be disseminated via scientific journal articles, editorials, press releases, oral presentations, conferences, encrypted email communications, and more. The communication plan can establish which means of communication are appropriate based on the information being shared.
Content
The communication plan can outline the types of information and level of detail that can be disseminated, and what information is to be omitted.
Dual-use potential and biosecurity concerns can impact what information scientists decide to convey in their communications. If the potential harm of publishing certain information outweighs the potential benefits, it is important to consider omitting it or refrain from publishing. For example, sensitive details, such as specific materials and methods, might be left out of a manuscript to protect information from adversaries. While omitting certain details may be part of responsible scientific communication when it comes to work involving pathogens or toxins with dual-use potential, sufficient details are still necessary to support the scientific integrity of the research.
The decision to omit sensitive information in published manuscripts is made by carefully considering the balance of scientific progress and protecting sensitive information from adversaries. The communication plan can facilitate decision-making regarding communications content, by identifying circumstances that would warrant the omission of information from a manuscript.
When preparing a manuscript for peer review and publication, researchers, the BSO, the IBC, and senior management can ask questions such as:
- How could the information be misused if published?
- Who might benefit from the research, and who could be harmed if the research was misused?
- Will the manuscript present sensitive information (e.g., genetic sequence of a modified virulence factor, process for altering the host range of a pathogen)?
- Should any sensitive information be removed prior to submission?
- Should the manuscript include a section describing the additional biosecurity measures implemented to mitigate the dual-use potential of the research project (e.g., review by biosecurity committee)?
- Does the publisher screen manuscripts for dual-use potential and could their reviewers assist in determining which information, if any, should be omitted?
In addition, it is recommended to alert journal editors, reviewers, or relevant advisory boards of any content that may be associated with dual-use potential.
3.3.3 Experimental Design Modifications
Experimental design modifications can allow for safer research without compromising research objectives. The following aspects of a research project may be modified to reduce dual-use potential:
Pathogen selection
It is preferable, especially from a dual-use potential perspective, to work with a less pathogenic alternative when comparable results can be achieved. For example, a pathogen with a broad environmental and host range might be:
- replaced by an attenuated strain that cannot grow well outside the laboratory environment or within humans
- replaced by an auxotrophic strain (i.e., unable to synthesize a substance needed for its growth)
- replaced by a component of a pathogen (e.g., a virus protein instead of a whole virus)
- inactivated (i.e., rendered completely non-infectious)
It is also important to consider whether research objectives can be met using a pathogen for which medical countermeasures (i.e., prophylactics, therapeutic treatments) are available. In general, there is a higher risk associated with pathogens that cause disease for which there are no treatments available. It is therefore recommended to:
- select a pathogen for which there are effective preventive or post-exposure therapies (e.g., vaccines, antiviral drugs)
- test the susceptibility of a pathogen to preventive or post-exposure therapies if there are no known countermeasures
Type of work
Along with appropriate biosecurity measures, in silico analysis (i.e., computer-based simulations, modeling, and data analysis) could be used instead of conducting in vivo or experiments. In silico analysis allows for detailed exploration of complex scenarios and is associated with fewer biosafety concerns, such as pathogen exposure during physical experimentation.Footnote41
Laboratory technique
Research objectives can sometimes be achieved using alternative laboratory techniques that are not associated with a risk of exposure or release. For example, antibody neutralization tests could be used instead of exposing experimental models to live pathogens.
3.4 Review and Continual Improvement
The degree of dual-use potential associated with a life science research project can change over time due to various factors, including new experimental findings, or the availability of new technologies. It is therefore recommended to continually review the dual-use potential associated with a project as part of a recurring review of the (CBS Matrix 4.1). This ongoing review is critical to identify and assess new, changing, or emerging risks, and to implement new or improved mitigation measures when needed.
The frequency of the biosecurity risk assessment review is influenced by the risks associated with the assets and activities. It could occur regularly, or as triggered by certain changes (e.g., upon the generation of unexpected results). When a biosecurity risk assessment is repeated or reviewed, it is important to update the biosecurity plan accordingly (CBS Matrix 4.1). The biosecurity plan is tailored to each facility and its level of detail and complexity will vary depending on the activities being conducted. For example, increased security measures are needed to work with pathogens and toxins determined to have increased dual-use potential (e.g., SSBAs). When an increase in dual-use potential is identified, repeating risk assessments helps determine whether new mitigation measures are necessary. Based on the biosecurity risk assessment, if the risks are deemed too high relative to the anticipated benefit, or if risk mitigation measures are not feasible, the project may need to be modified, or experiments could be moved to a facility with better risk mitigation capacity. In some cases, research may need to be stopped, or it may be paused until appropriate mitigation measures can be implemented.
Regularly discussing dual-use potential throughout a project can help identify hazards, assess risks, and facilitate the development of appropriate and adaptable risk mitigation measures. These discussions may include individuals and groups with relevant expertise, such as:
- licence or permit holder
- principal investigators
- internal or external collaborators
- research and laboratory personnel
- senior management
- the BSO
- the IBC
- security personnel
- ethicists
- funding agencies
- communications or public relations experts
- legal counsel
- relevant government departments and regulators
- representatives of the general public
The IBC is composed of members with various perspectives, such as laboratory personnel, medical professionals, senior management, and BSOs. Due to its role in biosafety program management and the range of expertise, skills, and knowledge afforded by diverse membership, an IBC is an excellent resource to perform or support risk assessments without overly restricting the research. If appropriately trained to identify risks, laboratory personnel and principal investigators can also be involved in the risk assessment process, as they will have the most knowledge about the planned research, potential findings, and contributions.
Input from representatives of the public can provide insight into how a research project is perceived, which can guide the development of a communication plan to address public concerns when research findings are published. Failure to review research projects from a dual-use potential perspective with a wide variety of stakeholders may increase the likelihood for misuse of resulting material or information.
back to topChapter 4 - Opportunities for Risk Management Throughout a Research Project
It is important to assess dual-use potential and implement risk management strategies throughout a research project. This chapter outlines how each stage of a research project provides an opportunity for risk management associated with dual-use potential.
4.1 Capacity and Infrastructure Assessment
It is critical that organizations have sufficient capacity and infrastructure to accommodate research associated with dual-use potential before the project begins. This includes having qualified personnel, internal oversight, appropriate physical design, established , and the equipment necessary to mitigate the risks associated with the dual-use potential. Given the increased digitization of research projects as well as increased targeting of the health sector by adversaries, it is important to have adequate cybersecurity infrastructure to secure the project throughout its lifecycle. It is therefore important that organizations assess whether the existing capacity and infrastructure can accommodate new research activities, and whether the mitigation measures in place are sufficient.
Training, development, and continuing education help equip personnel with the knowledge needed to assess the risks, benefits, and broader social implications of life science research. Most research personnel hired by an organization will likely possess a base level of dual-use potential knowledge as learned throughout high school, post-secondary education, internships, or science, technology, engineering and mathematics (STEM) competitions. However, organizations can provide staff with tailored training programs and continuing education opportunities to strengthen their understanding of dual-use potential. Codes of conduct and SOPs can also support the capacity of an organization’s personnel to sufficiently mitigate risks associated with dual-use potential. Committees trained in risk management and research ethics can be established to provide guidance and administrative oversight.
Given the multidisciplinary and sometimes converging nature of scientific research and innovation, it is important to extend education on dual-use potential to personnel such as engineers, computer scientists, and social scientists. Educational outreach in such fields can be structured through organizational training, or as a part of research collaborations, but may also occur through informal knowledge sharing.
4.2 Project Planning
Dual-use potential can be assessed long before research is initiated in the laboratory. The overall project concept and plan can be assessed to identify dual-use potential, appropriate mitigation measures, and modifications to lower the risks.
The goal of assessing dual-use potential at the planning stage is to establish a risk profile and determine whether it falls within the organization’s risk tolerance and complies with applicable legislation and regulations. Ideally, assessment of dual-use potential is conducted by individuals with different expertise, perspectives, and responsibilities. For example, while researchers have the most knowledge of their work and are in a key position to weigh the potential harms and benefits of their projects, their perspectives may be biased.
When scientific research is cross-disciplinary, multiple stakeholders and sectors work collaboratively to conduct research. In such cases, scientists, organizations, funding bodies, editors, and policy makers in private or public sectors can share the responsibility for mitigating the risks associated with research. The World Health Organization (WHO) provides checklists for various stakeholders throughout the research continuum to assist in managing risks associated with dual-use potential.Footnote1
4.3 Approval and Funding
Before research with dual-use potential is approved, it is important that the research proposal be reviewed by personnel from organizational bodies trained in risk management (e.g., the IBC, internal funding review panel, research security office), senior management, and the BSO. These individuals can collaborate to assess whether risks associated with dual-use potential are sufficiently managed before funding is granted by the organization or a grant application is submitted to funding agencies.
Throughout the approval process, it is important to be aware of any agreements in place regarding dual-use potential. This may include agreements with external non-regulatory bodies such as funding agencies and publishers, or internal oversight bodies or individuals, like the IBC, BSO, and laboratory personnel. Universities and affiliated research institutions who rely on funding from federal granting agencies must comply with the Government of Canada’s Policy on Sensitive Technology Research and Affiliations of Concern and the National Security Guidelines for Research Partnerships, where applicable.Footnote42,Footnote43 The policy prohibits federal funding to projects that aim to advance sensitive technology research areas if any of the researchers involved are affiliated with, or receive funding or in-kind support from, certain research organizations that could pose a risk to Canada’s national security (i.e., on the list of Named Research Organizations).Footnote44,Footnote45 The guidelines help researchers, research organizations, and federal funding organizations mitigate potential national security risks that may be associated with research partnerships.
It is important that organizations distributing funds to several researchers develop policies and guidelines to govern the administration of funds. Policies and guidelines can also be developed to clearly indicate how to identify and communicate risks and mitigation strategies. They inform the review and approval of research proposals before they are submitted to a funding agency. Discussions between individual researchers and organizational funding administrators can address concerns as well as clarify components of the research proposal, including dual-use potential and mitigation strategies.
4.4 Research
At times, dual-use potential may only become evident as an in-depth literature review progresses or when results are generated. It is therefore recommended to reassess the risk profile and existing mitigation measures when new information becomes available. It may be necessary to adjust the study design (e.g., experimental protocol) or the mitigation measures if an increase in dual-use potential is identified.
4.5 Results
The ethical responsibility of scientists extends to the result sharing stage with the wider scientific community or with the general public. The results of a research project can be assessed for dual-use potential prior to submitting for publication (e.g., a manuscript, a patent), during peer review, or even after publication. Mitigating risks associated with dual-use potential at this stage is most effective when all relevant stakeholders collaborate to evaluate results. This may include senior management, researchers, the IBC, editorial committees, and regulatory bodies.
back to topChapter 5 - References and Resources
Australia Group. (2023). List of Human and Animal Pathogens and Toxins for Export Control. Retrieved 2026-01-07 from https://www.dfat.gov.au/publications/minisite/theaustraliagroupnet/site/en/human_animal_pathogens.html
Cello, J., Paul, A. V., & Wimmer, E. (2002). Chemical Synthesis of Poliovirus cDNA: Generation of Infectious Virus in the Absence of Natural Template. Science, 297(5583): 1016-1018.
Centers for Disease Control and Prevention (United States). (2005). Researchers Reconstruct 1918 Pandemic Influenza Virus; Effort Designed to Advance Preparedness. ScienceDaily. Retrieved 2026-01-07 from https://www.sciencedaily.com/releases/2005/10/051005230557.htm
Cole, J., Morris, P., Dickman, M. J., & Dockrell, D. H. (2016). The Therapeutic Potential of Epigenetic Manipulation During Infectious Diseases. Pharmacology & Therapeutics, 167: 85-99.
Debmalya, B., Vijender, C., Eugenia, C. Y., Emmanuel, O. S., Sudhir, C., et al. (2014). In Silico Models: From Simple Networks to Complex Diseases. In Ashish, S. V., & Anchal, S. (Eds.), Animal Biotechnology (pp. 385-404). San Diego, California, USA: Academic Press.
Export and Import Permits Act (R.S.C., 1985, c. E-19).
Export Control List (SOR/89-202).
Federal Bureau of Investigation (United States). Amerithrax. Retrieved 2026-01-07 from https://vault.fbi.gov/Amerithrax
Government of Canada. (2015). Plan for Administrative Oversight for Pathogens and Toxins in a Research Setting – Required Elements and Guidance. Ottawa, ON, Canada: Government of Canada. Available from https://www.canada.ca/en/public-health/services/laboratory-biosafety-biosecurity/licensing-program/plan-administrative-oversight-pathogens-toxins-a-research-setting-required-elements-guidance.html
Government of Canada. (2018). Canadian Biosafety Guideline – Conducting a Biosecurity Risk Assessment. Ottawa, ON, Canada: Government of Canada. Available from https://www.canada.ca/en/public-health/services/canadian-biosafety-standards-guidelines/guidance.html
Government of Canada. (2018). Canadian Biosafety Guideline – Pathogen Risk Assessment. Ottawa, ON, Canada: Government of Canada. Available from https://www.canada.ca/en/public-health/services/canadian-biosafety-standards-guidelines/guidance.html
Government of Canada. (2021). Scientific Research Policy for Human Pathogens and Toxins. Available from https://www.canada.ca/en/public-health/services/laboratory-biosafety-biosecurity/scientific-research-policy-human-pathogens-toxins.html
Government of Canada. (2022). Canadian Biosafety Standard (3rd ed.). Ottawa, ON, Canada: Government of Canada. Available from https://www.canada.ca/en/public-health/services/canadian-biosafety-standards-guidelines/third-edition.html
Government of Canada. (2024). Biosecurity Addendum to the Canadian Biosafety Standard, Third Edition. Ottawa, ON, Canada: Government of Canada. Available from https://training-formation.phac-aspc.gc.ca/mod/page/view.php?id=16281
Government of Canada. (2024). Canada and the International Health Regulations (IHR): Overview. Available from https://www.canada.ca/en/public-health/services/emergency-preparedness-response/international-health-regulations.html
Government of Canada. (2024). The Cyber Threat to Research Laboratories. Ottawa, ON, Canada: Government of Canada. Available from https://www.cyber.gc.ca/en/guidance/cyber-threat-research-laboratories
Government of Canada. (2024). Named Research Organizations. Ottawa, ON, Canada: Government of Canada. Available from https://science.gc.ca/site/science/en/safeguarding-your-research/guidelines-and-tools-implement-research-security/sensitive-technology-research-and-affiliations-concern/named-research-organizations
Government of Canada. (2024). Policy on Sensitive Technology Research and Affiliations of Concern. Ottawa, ON, Canada: Government of Canada. Available from https://science.gc.ca/site/science/en/safeguarding-your-research/guidelines-and-tools-implement-research-security/sensitive-technology-research-and-affiliations-concern/policy-sensitive-technology-research-and-affiliations-concern
Government of Canada. (2024). Policy Statements. Available from https://science.gc.ca/site/science/en/safeguarding-your-research/general-information-research-security/additional-resources/policy-statements
Government of Canada. (2024). Sensitive Technology Research Areas. Available from https://science.gc.ca/site/science/en/safeguarding-your-research/guidelines-and-tools-implement-research-security/sensitive-technology-research-and-affiliations-concern/sensitive-technology-research-areas
Government of Canada. (2025). A Guide to Canada’s Export Control List. Ottawa, ON, Canada: Government of Canada. Available from https://www.international.gc.ca/trade-commerce/controls-controles/ecl-lec/index.aspx?lang=eng
Government of Canada. (2025). National Security Guidelines for Research Partnerships. Ottawa, ON, Canada: Government of Canada. Available from https://science.gc.ca/site/science/en/safeguarding-your-research/guidelines-and-tools-implement-research-security/national-security-guidelines-research-partnerships
Government of Canada. (2025). Sensitive Technology List. Available from https://www.canada.ca/en/services/defence/nationalsecurity/sensitive-technology-list.html
Health of Animals Act (S.C. 1990, c. 21).
Health of Animals Regulations (C.R.C., c. 296).
Herfst, S., Schrauwen, E. J., Linster, M., Chutinimitkul, S., de Wit, E., et al. (2012). Airborne Transmission of Influenza A/H5N1 Virus Between Ferrets. Science, 336(6088): 1534-1541.
Human Pathogens and Toxins Act (S.C. 2009, c. 24).
Human Pathogens and Toxins Regulations (SOR/2015-44).
Imai, M., Watanabe, T., Hatta, M., Das, S. C., Ozawa, M., et al. (2012). Experimental Adaptation of an Influenza H5 HA Confers Respiratory Droplet Transmission to a Reassortant H5 HA/H1N1 Virus in Ferrets. Nature, 486(7403): 420-428.
International Organization for Standardization. (2020). ISO 35001:2019, Biorisk management for laboratories and other related organisations. Geneva, Switzerland: International Organization for Standardization.
Licht, J. D., & Bennett, R. L. (2021). Leveraging Epigenetics to Enhance the Efficacy of Immunotherapy. Clinical Epigenetics, 13(1): 115.
Mansfield, M. J., Wentz, T. G., Zhang, S., Lee, E. J., Dong, M., et al. (2019). Bioinformatic Discovery of a Toxin Family in Chryseobacterium piperi with Sequence Similarity to Botulinum Neurotoxins. Science Reports, 9(1): 1634.
McMullan, L. K., Flint, M., Chakrabarti, A., Guerrero, L., Lo, M. K., et al. (2019). Characterisation of Infectious Ebola Virus from the Ongoing Outbreak to Guide Response Activities in the Democratic Republic of the Congo: A Phylogenetic and In Vitro Analysis. The Lancet Infectious Diseases, 19(9): 1023-1032.
National Academies of Sciences, Engineering and Medicine (United States). (2017). Managing Dual Use Research of Concern. In Dual Use Research of Concern in the Life Sciences: Current Issues and Controversies (pp. 45-72). Washington, DC, USA: National Academies Press.
National Research Council of the National Academies (United States). (2015). Gain-of-Function Research: Background and Alternatives. In Potential Risks and Benefits of Gain-of-Function Research: Summary of a Workshop (pp. 21-28). Washington, DC, USA: National Academies Press.
Negi, S. S., Schein, C. H., Ladics, G. S., Mirsky, H., Chang, P., et al. (2017). Functional Classification of Protein Toxins as a Basis for Bioinformatic Screening. Scientific Reports, 7(1): 13940.
Noyce, R. S., Lederman, S., & Evans, D. H. (2018). Construction of an Infectious Horsepox Virus Vaccine from Chemically Synthesized DNA Fragments. Public Library of Science One, 13(1): e0188453.
Rosengard, A. M., Liu, Y., Nie, Z., & Jimenez, R. (2002). Variola Virus Immune Evasion Design: Expression of a Highly Efficient Inhibitor of Human Complement. Proceedings of the National Academy of Sciences of the United States of America, 99(13): 8808-8813.
Satyanarayana, K. (2011). Dual Dual-Use Research of Concern: Publish and Perish? Indian Journal of Medical Research, 133(1): 1-4.
Schuerger, C., Batalis, S., Quinn, K., Kinoshita, R., Daniels, O. J., & Puglisi, A. (2023). Understanding the Global Gain-of-Function Research Landscape. Center for Security and Emerging Technology. Retrieved 2025-05-22 from https://cset.georgetown.edu/publication/understanding-the-global-gain-of-function-research-landscape/
Tumpey, T. M., Basler, C. F., Aguilar, P. V., Zeng, H., Solórzano, A., et al. (2005). Characterization of the Reconstructed 1918 Spanish Influenza Pandemic Virus. Science, 310(5745): 77-80.
United Nations Office for Disarmament Affairs. (1975). The Convention on the Prohibition of the Development, Production and Stockpiling of Bacteriological (Biological) and Toxin Weapons and on their Destruction. Retrieved 2025-03-05 from https://front.un-arm.org/wp-content/uploads/2020/12/BWC-text-English-1.pdf
United Nations Security Council. (2004). Resolution 1540. United Nations Security Council. Retrieved 2025-03-05 from https://www.un.org/en/sc/1540/resolutions-committee-reports-and-SC-briefings/security-council-resolutions.shtml
Urbina, F., Lentzos, F., Invernizzi, C., & Ekins, S. (2022). Dual Use of Artificial-Intelligence-Powered Drug Discovery. Nature Machine Intelligence, 4(3): 189-191.
Warrick, J. (2010). FBI Investigation of 2001 Anthrax Attacks Concluded; U.S. Releases Details. Washington Post. Retrieved 2026-01-07 from https://www.washingtonpost.com/wp-dyn/content/article/2010/02/19/AR2010021902369.html
Wassenaar Arrangement. (1996). The Wassenaar Arrangement on Export Controls for Conventional Arms and Dual-Use Goods and Technologies. Retrieved 2025-06-11 from https://www.wassenaar.org/
Wishart, D., Arndt, D., Pon, A., Sajed, T., Guo, A. C., et al. (2015). T3DB: the Toxic Exposome Database. Nucleic Acids Research, 43(Database issue): D928-934.
World Health Organization. (2016). International Health Regulations (2005) (3rd ed.). Geneva, Switzerland: WHO Press.
World Health Organization. (2022). Global Guidance Framework For the Responsible Use of the Life Sciences: Mitigating Biorisks and Governing Dual-Use Research. World Health Organization. Retrieved 2026-01-07 from https://www.who.int/publications/i/item/9789240056107
World Health Organization. (2024). Laboratory Biosecurity Guidance. World Health Organization. Retrieved 2025-06-11 from https://www.who.int/publications/i/item/9789240095113
World Health Organization. (2025). International Health Regulations. Retrieved 2025-06-11 from https://www.who.int/health-topics/international-health-regulations/#tab=tab_2
Xie, X., Lokugamage, K. G., Zhang, X., Vu, M. N., Muruato, A. E., et al. (2021). Engineering SARS-CoV-2 Using a Reverse Genetic System. Nature Protocols, 16(3): 1761-1784.
Zarzeczny, A., & Caulfield, T. (2009). Emerging Ethical, Legal and Social Issues Associated with Stem Cell Research and the Current Role of the Moral Status of the Embryo. Stem Cell Reviews and Reports, 5(2): 96-101.
Additional Resources
Biosecurity Office (Netherlands). Dual-Use Quickscan. Retrieved 2026-01-07 from https://dualusequickscan.com/en/
Georgetown University. Biosecurity Central. Retrieved 2026-01-07 from https://www.biosecuritycentral.org/
Government of Canada. Tri-agency guidance on research security. Available from https://www.nserc-crsng.gc.ca/InterAgency-Interorganismes/RS-SR/index_eng.asp
Government of Canada. (2016). Canadian Biosafety Guideline – Developing a Comprehensive Biosecurity Plan. Ottawa, ON, Canada: Government of Canada. Available from https://www.canada.ca/en/public-health/services/canadian-biosafety-standards-guidelines/guidance.html
Government of Canada. (2017). Canadian Biosafety Guideline – Notification and Reporting Under the HPTA and HPTR. Ottawa, ON, Canada: Government of Canada. Available from https://www.canada.ca/en/public-health/services/canadian-biosafety-standards-guidelines/guidance.html
Government of Canada. (2018). Canadian Biosafety Guideline – Local Risk Assessment. Ottawa, ON, Canada: Government of Canada. Available from https://www.canada.ca/en/public-health/services/canadian-biosafety-standards-guidelines/guidance.html
Government of Canada. (2022). Effective Management of Dual-Use in Life Sciences Research (March 23, 2022). Available from https://training-formation.phac-aspc.gc.ca/enrol/index.php?id=493
Government of Canada. (2022). Safeguarding Your Research. Available from https://science.gc.ca/site/science/en/safeguarding-your-research
Government of Canada. (2023). Introducing Biosecurity. Available from https://training-formation.phac-aspc.gc.ca/course/view.php?id=6
Government of Canada. (2023). Introduction to Dual-Use in Life Sciences Research. Available from https://training-formation.phac-aspc.gc.ca/course/view.php?id=110
Government of Canada. (2023). Memorandum D19-9-4: Importation and Exportation of Pathogens and Toxins. Ottawa, ON, Canada: Government of Canada. Available from https://www.cbsa-asfc.gc.ca/publications/dm-md/d19/d19-9-4-eng.html
Government of Canada. (2024). Biosecurity. Available from https://www.canada.ca/en/public-health/services/laboratory-biosafety-biosecurity/biosecurity.html
Government of Canada. (2024). Research Security. Available from https://www.canada.ca/en/services/defence/researchsecurity/about.html
Government of Canada. (2024). Safeguarding Science Webinar (June 19, 2024). Available from https://training-formation.phac-aspc.gc.ca/course/view.php?id=712
Government of Canada. (2025). Safeguarding Science. Available from https://www.publicsafety.gc.ca/cnt/ntnl-scrt/cntr-trrrsm/cntr-prlfrtn/sfgrdng-scnc/sfgrdng-scnc-wrkshp-en.aspx
World Health Organization. Ensuring responsible use of life sciences research. World Health Organization. Retrieved 2025-07-16 from https://www.who.int/activities/ensuring-responsible-use-of-life-sciences-research
back to topAppendix A – International Initiatives Related to Dual-Use Potential
Canada is part of multiple international initiatives for the control of dual-use goods, which are reflected in Canadian legislation and policies. Many international initiatives aim to identify and mitigate the risks associated with biological research, and provide the current global context on dual-use potential.
Australia Group
The Australia Group is an informal arrangement that aims to harmonize export controls to prevent exports from contributing to the development and proliferation of chemical and biological weapons. It was formed in 1985 and consists of 43 member countries, including Canada. In the 1990s, biological agents with dual-use potential were added to export control lists developed by the Australia Group. Canada implements the Australia Group’s common control list entitled List of Human and Animal Pathogens and Toxins for Export Control through the Export and Import Permits Act.Footnote22 In addition, this common control list is incorporated by reference into the HPTR as one criterion for a prescribed human pathogen or toxin (i.e., SSBA) in Canada.Footnote46
Biological Weapons Convention
Internationally, since 1975, State Parties have agreed to not deliberately develop microbial agents as a biological weapon as part of the Convention on the Prohibition of the Development, Production and Stockpiling of Bacteriological (Biological) and Toxin Weapons and on their Destruction. Specifically, Article I of the Convention states:
“Each State Party to this Convention undertakes never in any circumstances to develop, produce, stockpile or otherwise acquire to retain:
(1) microbial or other biological agents, or toxins whatever their origin or method of production, of types and in quantities that have no justification for prophylactic, protective or other peaceful purposes;
(2) weapons, equipment or means of delivery designed to use such agents or toxins for hostile purposes or in armed conflict.”Footnote47
The Convention is a key element in the international community’s efforts to address the proliferation of weapons of mass destruction. The Convention has been adopted by 188 states, including Canada.
International Health Regulations
The International Health Regulations (IHR) require 196 countries, including Canada, to work together to prevent, protect against, control, and respond to the international spread of disease without unnecessarily interfering with international traffic and trade.Footnote48 The IHR provides a framework for managing potential international public health events and emergencies. Countries are required to develop, strengthen, and maintain specific core capacities including the following:Footnote49
- national surveillance to detect potential public health threats
- assessment of public health events within their territory
- notification and reporting to WHO of public health events within their territory that may pose a public health emergency of international concern
- response to public health risks and emergencies
Additionally, when feasible, countries are required to report to WHO within 24 hours of receipt of evidence of a public health risk identified outside their territory that may cause international disease spread.Footnote50
United Nations Security Council Resolution 1540
The United Nations Security Council Resolution 1540 was adopted in 2004 to prevent the development of biological and other weapons and related materials.Footnote51 The resolution requires all 193 United Nations Member States to adopt and enforce appropriate laws to this effect as well as other effective measures to prevent the proliferation of these weapons and their means of delivery to prevent non-State actors gaining access to them, in particular for terrorist purposes. Members of the United Nations, including Canada, must report on their compliance.
The Security Council Committee that was established in accordance with Resolution 1540 is responsible for reporting on the implementation of this resolution to the Security Council. The United Nations Office for Disarmament Affairs (UNODA) supports the activities of this Committee and aims to promote multilateral efforts with the goal of achieving complete disarmament. This includes:
- supporting regional cooperation to facilitate national implementation activities
- promoting cooperation between international, regional, and sub-regional organizations
- cultivating effective partnerships between key stakeholders including civil society, private sector, and academia
Wassenaar Arrangement
The Wassenaar Arrangement on Export Controls for Conventional Arms and Dual-Use Goods and Technologies, commonly known as the Wassenaar Arrangement, was established in 1996. One of its objectives is to contribute to regional and international security and stability by promoting voluntary transparency and greater responsibility in transfers of conventional arms and dual-use goods and technologies, thus preventing destabilizing accumulations.Footnote52 Participating States seek, through their national policies, to ensure that transfers of such items do not contribute to the development or enhancement of military capabilities that undermine the goals of the arrangement, and are not diverted to support such capabilities. Currently, there are 42 Participating States, including Canada.
World Health Organization
With 194 Members States, one of the goals of the WHO is to promote responsible and innovative life science research on a global level. This is achieved by various means, including hosting events, meetings, and workshops, and publishing guidance documents and newsletters. For example, WHO has published guidance and frameworks on effective risk management and laboratory biosecurity. WHO describes research with biological material that could have severe or catastrophic consequences to life as “high-consequence research”.Footnote53
back to topReferences
- Footnote 1
-
World Health Organization. (2022). Global Guidance Framework For the Responsible Use of the Life Sciences: Mitigating Biorisks and Governing Dual-Use Research. World Health Organization. Retrieved 2026-01-07 from https://www.who.int/publications/i/item/9789240056107
- Footnote 2
-
National Academies of Sciences, Engineering and Medicine (United States). (2017). Managing Dual Use Research of Concern. In Dual Use Research of Concern in the Life Sciences: Current Issues and Controversies (pp. 45-72). Washington, DC, USA: National Academies Press.
- Footnote 3
-
Federal Bureau of Investigation (United States). Amerithrax. Retrieved 2026-01-07 from https://vault.fbi.gov/Amerithrax
- Footnote 4
-
Warrick, J. (2010). FBI Investigation of 2001 Anthrax Attacks Concluded; U.S. Releases Details. Washington Post. Retrieved 2026-01-07 from https://www.washingtonpost.com/wp-dyn/content/article/2010/02/19/AR2010021902369.html
- Footnote 5
-
Satyanarayana, K. (2011). Dual Dual-Use Research of Concern: Publish and Perish? Indian Journal of Medical Research, 133(1): 1-4.
- Footnote 6
-
Zarzeczny, A., & Caulfield, T. (2009). Emerging Ethical, Legal and Social Issues Associated with Stem Cell Research and the Current Role of the Moral Status of the Embryo. Stem Cell Reviews and Reports, 5(2): 96-101.
- Footnote 7
-
National Research Council of the National Academies (United States). (2015). Gain-of-Function Research: Background and Alternatives. In Potential Risks and Benefits of Gain-of-Function Research: Summary of a Workshop (pp. 21-28). Washington, DC, USA: National Academies Press.
- Footnote 8
-
Cello, J., Paul, A. V., & Wimmer, E. (2002). Chemical Synthesis of Poliovirus cDNA: Generation of Infectious Virus in the Absence of Natural Template. Science, 297(5583): 1016-1018.
- Footnote 9
-
Rosengard, A. M., Liu, Y., Nie, Z., & Jimenez, R. (2002). Variola Virus Immune Evasion Design: Expression of a Highly Efficient Inhibitor of Human Complement. Proceedings of the National Academy of Sciences of the United States of America, 99(13): 8808-8813.
- Footnote 10
-
Tumpey, T. M., Basler, C. F., Aguilar, P. V., Zeng, H., Solórzano, A., et al. (2005). Characterization of the Reconstructed 1918 Spanish Influenza Pandemic Virus. Science, 310(5745): 77-80.
- Footnote 11
-
Centers for Disease Control and Prevention (United States). (2005). Researchers Reconstruct 1918 Pandemic Influenza Virus; Effort Designed to Advance Preparedness. ScienceDaily. Retrieved 2026-01-07 from https://www.sciencedaily.com/releases/2005/10/051005230557.htm
- Footnote 12
-
Imai, M., Watanabe, T., Hatta, M., Das, S. C., Ozawa, M., et al. (2012). Experimental Adaptation of an Influenza H5 HA Confers Respiratory Droplet Transmission to a Reassortant H5 HA/H1N1 Virus in Ferrets. Nature, 486(7403): 420-428.
- Footnote 13
-
Herfst, S., Schrauwen, E. J., Linster, M., Chutinimitkul, S., de Wit, E., et al. (2012). Airborne Transmission of Influenza A/H5N1 Virus Between Ferrets. Science, 336(6088): 1534-1541.
- Footnote 14
-
Noyce, R. S., Lederman, S., & Evans, D. H. (2018). Construction of an Infectious Horsepox Virus Vaccine from Chemically Synthesized DNA Fragments. Public Library of Science One, 13(1): e0188453.
- Footnote 15
-
McMullan, L. K., Flint, M., Chakrabarti, A., Guerrero, L., Lo, M. K., et al. (2019). Characterisation of Infectious Ebola Virus from the Ongoing Outbreak to Guide Response Activities in the Democratic Republic of the Congo: A Phylogenetic and In Vitro Analysis. The Lancet Infectious Diseases, 19(9): 1023-1032.
- Footnote 16
-
Xie, X., Lokugamage, K. G., Zhang, X., Vu, M. N., Muruato, A. E., et al. (2021). Engineering SARS-CoV-2 Using a Reverse Genetic System. Nature Protocols, 16(3): 1761-1784.
- Footnote 17
-
Human Pathogens and Toxins Act (S.C. 2009, c. 24).
- Footnote 18
-
Human Pathogens and Toxins Regulations (SOR/2015-44).
- Footnote 19
-
Health of Animals Act (S.C. 1990, c. 21).
- Footnote 20
-
Health of Animals Regulations (C.R.C., c. 296).
- Footnote 21
-
Government of Canada. (2022). Canadian Biosafety Standard (3rd ed.). Ottawa, ON, Canada: Government of Canada. Available from https://www.canada.ca/en/public-health/services/canadian-biosafety-standards-guidelines/third-edition.html
- Footnote 22
-
Export and Import Permits Act (R.S.C., 1985, c. E-19).
- Footnote 23
-
Export Control List (SOR/89-202).
- Footnote 24
-
Government of Canada. (2025). A Guide to Canada’s Export Control List. Ottawa, ON, Canada: Government of Canada. Available from https://www.international.gc.ca/trade-commerce/controls-controles/ecl-lec/index.aspx?lang=eng
- Footnote 25
-
Government of Canada. (2021). Scientific Research Policy for Human Pathogens and Toxins. Available from https://www.canada.ca/en/public-health/services/laboratory-biosafety-biosecurity/scientific-research-policy-human-pathogens-toxins.html
- Footnote 26
-
Government of Canada. (2015). Plan for Administrative Oversight for Pathogens and Toxins in a Research Setting – Required Elements and Guidance. Ottawa, ON, Canada: Government of Canada. Available from https://www.canada.ca/en/public-health/services/laboratory-biosafety-biosecurity/licensing-program/plan-administrative-oversight-pathogens-toxins-a-research-setting-required-elements-guidance.html
- Footnote 27
-
Government of Canada. (2025). Sensitive Technology List. Available from https://www.canada.ca/en/services/defence/nationalsecurity/sensitive-technology-list.html
- Footnote 28
-
Urbina, F., Lentzos, F., Invernizzi, C., & Ekins, S. (2022). Dual Use of Artificial-Intelligence-Powered Drug Discovery. Nature Machine Intelligence, 4(3): 189-191.
- Footnote 29
-
Schuerger, C., Batalis, S., Quinn, K., Kinoshita, R., Daniels, O. J., & Puglisi, A. (2023). Understanding the Global Gain-of-Function Research Landscape. Center for Security and Emerging Technology. Retrieved 2025-05-22 from https://cset.georgetown.edu/publication/understanding-the-global-gain-of-function-research-landscape/
- Footnote 30
-
Licht, J. D., & Bennett, R. L. (2021). Leveraging Epigenetics to Enhance the Efficacy of Immunotherapy. Clinical Epigenetics, 13(1): 115.
- Footnote 31
-
Cole, J., Morris, P., Dickman, M. J., & Dockrell, D. H. (2016). The Therapeutic Potential of Epigenetic Manipulation During Infectious Diseases. Pharmacology & Therapeutics, 167: 85-99.
- Footnote 32
-
Wishart, D., Arndt, D., Pon, A., Sajed, T., Guo, A. C., et al. (2015). T3DB: the Toxic Exposome Database. Nucleic Acids Research, 43(Database issue): D928-934.
- Footnote 33
-
Negi, S. S., Schein, C. H., Ladics, G. S., Mirsky, H., Chang, P., et al. (2017). Functional Classification of Protein Toxins as a Basis for Bioinformatic Screening. Scientific Reports, 7(1): 13940.
- Footnote 34
-
Mansfield, M. J., Wentz, T. G., Zhang, S., Lee, E. J., Dong, M., et al. (2019). Bioinformatic Discovery of a Toxin Family in Chryseobacterium piperi with Sequence Similarity to Botulinum Neurotoxins. Science Reports, 9(1): 1634.
- Footnote 35
-
Government of Canada. (2018). Canadian Biosafety Guideline – Pathogen Risk Assessment. Ottawa, ON, Canada: Government of Canada. Available from https://www.canada.ca/en/public-health/services/canadian-biosafety-standards-guidelines/guidance.html
- Footnote 36
-
Government of Canada. (2024). The Cyber Threat to Research Laboratories. Ottawa, ON, Canada: Government of Canada. Available from https://www.cyber.gc.ca/en/guidance/cyber-threat-research-laboratories
- Footnote 37
-
Government of Canada. (2024). Policy Statements. Available from https://science.gc.ca/site/science/en/safeguarding-your-research/general-information-research-security/additional-resources/policy-statements
- Footnote 38
-
Government of Canada. (2018). Canadian Biosafety Guideline – Conducting a Biosecurity Risk Assessment. Ottawa, ON, Canada: Government of Canada. Available from https://www.canada.ca/en/public-health/services/canadian-biosafety-standards-guidelines/guidance.html
- Footnote 39
-
International Organization for Standardization. (2020). ISO 35001:2019, Biorisk management for laboratories and other related organisations. Geneva, Switzerland: International Organization for Standardization.
- Footnote 40
-
Government of Canada. (2024). Biosecurity Addendum to the Canadian Biosafety Standard, Third Edition. Ottawa, ON, Canada: Government of Canada. Available from https://training-formation.phac-aspc.gc.ca/mod/page/view.php?id=16281
- Footnote 41
-
Debmalya, B., Vijender, C., Eugenia, C. Y., Emmanuel, O. S., Sudhir, C., et al. (2014). In Silico Models: From Simple Networks to Complex Diseases. In Ashish, S. V., & Anchal, S. (Eds.), Animal Biotechnology (pp. 385-404). San Diego, California, USA: Academic Press.
- Footnote 42
-
Government of Canada. (2024). Policy on Sensitive Technology Research and Affiliations of Concern. Ottawa, ON, Canada: Government of Canada. Available from https://science.gc.ca/site/science/en/safeguarding-your-research/guidelines-and-tools-implement-research-security/sensitive-technology-research-and-affiliations-concern/policy-sensitive-technology-research-and-affiliations-concern
- Footnote 43
-
Government of Canada. (2025). National Security Guidelines for Research Partnerships. Ottawa, ON, Canada: Government of Canada. Available from https://science.gc.ca/site/science/en/safeguarding-your-research/guidelines-and-tools-implement-research-security/national-security-guidelines-research-partnerships
- Footnote 44
-
Government of Canada. (2024). Sensitive Technology Research Areas. Available from https://science.gc.ca/site/science/en/safeguarding-your-research/guidelines-and-tools-implement-research-security/sensitive-technology-research-and-affiliations-concern/sensitive-technology-research-areas
- Footnote 45
-
Government of Canada. (2024). Named Research Organizations. Ottawa, ON, Canada: Government of Canada. Available from https://science.gc.ca/site/science/en/safeguarding-your-research/guidelines-and-tools-implement-research-security/sensitive-technology-research-and-affiliations-concern/named-research-organizations
- Footnote 46
-
Australia Group. (2023). List of Human and Animal Pathogens and Toxins for Export Control. Retrieved 2026-01-07 from https://www.dfat.gov.au/publications/minisite/theaustraliagroupnet/site/en/human_animal_pathogens.html
- Footnote 47
-
United Nations Office for Disarmament Affairs. (1975). The Convention on the Prohibition of the Development, Production and Stockpiling of Bacteriological (Biological) and Toxin Weapons and on their Destruction. Retrieved 2025-03-05 from https://front.un-arm.org/wp-content/uploads/2020/12/BWC-text-English-1.pdf
- Footnote 48
-
Government of Canada. (2024). Canada and the International Health Regulations (IHR): Overview. Available from https://www.canada.ca/en/public-health/services/emergency-preparedness-response/international-health-regulations.html
- Footnote 49
-
World Health Organization. (2025). International Health Regulations. Retrieved 2025-06-11 from https://www.who.int/health-topics/international-health-regulations/#tab=tab_2
- Footnote 50
-
World Health Organization. (2016). International Health Regulations (2005) (3rd ed.). Geneva, Switzerland: WHO Press.
- Footnote 51
-
United Nations Security Council. (2004). Resolution 1540. United Nations Security Council. Retrieved 2025-03-05 from https://www.un.org/en/sc/1540/resolutions-committee-reports-and-SC-briefings/security-council-resolutions.shtml
- Footnote 52
-
Wassenaar Arrangement. (1996). The Wassenaar Arrangement on Export Controls for Conventional Arms and Dual-Use Goods and Technologies. Retrieved 2025-06-11 from https://www.wassenaar.org/
- Footnote 53
-
World Health Organization. (2024). Laboratory Biosecurity Guidance. World Health Organization. Retrieved 2025-06-11 from https://www.who.int/publications/i/item/9789240095113
